Section 2 – Implement a Security Extension of a Layer 2 solution, given a network design and a set of requirements
QUESTION NO: 21
The Company security administrator is concerned with layer 2 network attacks. Which two statements about these attacks are true? (Select two)
A. ARP spoofing attacks are attempts to redirect traffic to an attacking host by encapsulating a false 802.1Q header on a frame and causing traffic to be delivered to the wrong VLAN.
B. ARP spoofing attacks are attempts to redirect traffic to an attacking host by sending an ARP message with a forged identity to a transmitting host.
C. MAC address flooding is an attempt to force a switch to send all information out every port by overloading the MAC address table.
D. ARP spoofing attacks are attempts to redirect traffic to an attacking host by sending an ARP packet that contains the forged address of the next hop router.
E. MAC address flooding is an attempt to redirect traffic to a single port by associating that port with all MAC addresses in the VLAN.
Answer: B,C
QUESTION NO: 22
Refer to the exhibit. What will happen to traffic within VLAN 14 with a source address of 172.16.10.5?
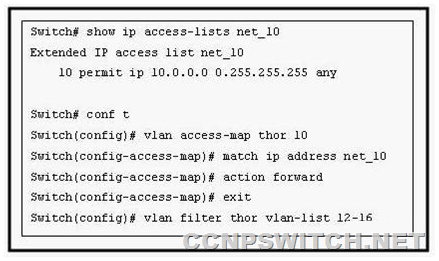
A. The traffic will be forwarded to the router processor for further processing.
B. The traffic will be dropped.
C. The traffic will be forwarded to the TCAM for further processing.
D. The traffic will be forwarded without further processing.
Answer: B
Explanation:
VLAN maps, also known as VLAN ACLs or VACLs, can filter all traffic traversing a switch. VLAN maps can be configured on the switch to filter all packets that are routed into or out of a VLAN, or are bridged within a VLAN. VLAN maps are used strictly for security packet filtering. Unlike router ACLs, VLAN maps are not defined by direction (input or output).
To create a VLAN map and apply it to one or more VLANs, perform these steps: Create the standard or extended IP ACLs or named MAC extended ACLs to be applied to the VLAN. This access-list will select the traffic that will be either forwarded or dropped by the access-map. Only traffic matching the ‘permit’ condition in an access-list will be passed to the access-map for further processing. Enter the vlan access-map access-map-name [ sequence ] global configuration command to create a VLAN ACL map entry. Each access-map can have multiple entries. The order of these entries is determined by the sequence . If no sequence number is entered, accessmap entries are added with sequence numbers in increments of 10. In access map configuration mode, optionally enter an action forward or action drop . The default is to forward traffic. Also enter the match command to specify an IP packet or a non-IP packet (with only a known MAC address), and to match the packet against one or more ACLs (standard or extended). Use the vlan filter access-map-name vlan-list vlan-list global configuration command to apply a VLAN map to one or more VLANs. A single access-map can be used on multiple VLANs.
QUESTION NO: 23
Switch R1 has been configured with Private VLANs. With that type of PVLAN port should the default gateway be configured?
A. Trunk
B. Isolated
C. Primary
D. Community
E. Promiscuous
F. None of the other alternatives apply
Answer: E
Explanation:
Promiscuous: The switch port connects to a router, firewall, or other common gateway device. This port can communicate with anything else connected to the primary or any secondary VLAN.
In other words, the port is in promiscuous mode, in which the rules of private VLANs are ignored.
QUESTION NO: 24
Refer to the exhibit. An attacker is connected to interface Fa0/11 on switch A-SW2 and attempts to establish a DHCP server for a man-in-middle attack. Which recommendation, if followed, would mitigate this type of attack?
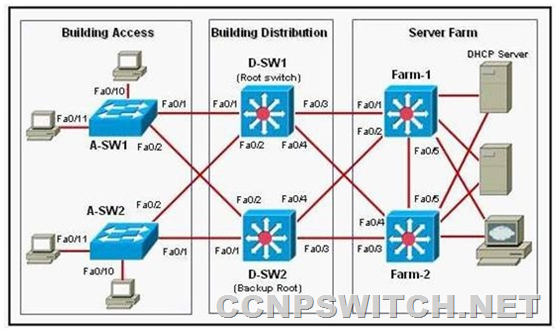
A. All switch ports in the Building Access block should be configured as DHCP untrusted ports.
B. All switch ports in the Building Access block should be configured as DHCP trusted ports.
C. All switch ports connecting to servers in the Server Farm block should be configured as DHCP untrusted ports.
D. All switch ports connecting to hosts in the Building Access block should be configured as DHCP trusted ports.
E. All switch ports in the Server Farm block should be configured as DHCP untrusted ports.
F. All switch ports connecting to hosts in the Building Access block should be configured as DHCP untrusted ports.
Answer: F
Explanation:
One of the ways that an attacker can gain access to network traffic is to spoof responses that would be sent by a valid DHCP server. The DHCP spoofing device replies to client DHCP requests. The legitimate server may reply also, but if the spoofing device is on the same segment as the client, its reply to the client may arrive first.
The intruder’s DHCP reply offers an IP address and supporting information that designates the intruder as the default gateway or Domain Name System (DNS) server. In the case of a gateway, the clients will then forward packets to the attacking device, which will in turn send them to the desired destination. This is referred to as a "man-in-the-middle" attack, and it may go entirely undetected as the intruder intercepts the data flow through the network.
Untrusted ports are those that are not explicitly configured as trusted. A DHCP binding table is built for untrusted ports. Each entry contains the client MAC address, IP address, lease time, binding type, VLAN number, and port ID recorded as clients make DHCP requests. The table is then used to filter subsequent DHCP traffic. From a DHCP snooping perspective, untrusted access ports should not send any DHCP server responses, such as DHCPOFFER, DHCPACK, DHCPNAK.
QUESTION NO: 25
VLAN maps have been configured on switch R1. Which of the following actions are taken in a VLAN map that does not contain a match clause?
A. Implicit deny feature at end of list.
B. Implicit deny feature at start of list.
C. Implicit forward feature at end of list
D. Implicit forward feature at start of list.
Answer: A
Explanation:
Each VLAN access map can consist of one or more map sequences, each sequence with a match clause and an action clause. The match clause specifies IP, IPX, or MAC ACLs for traffic filtering and the action clause specifies the action to be taken when a match occurs. When a flow matches a permit ACL entry the associated action is taken and the flow is not checked against the remaining sequences. When a flow matches a deny ACL entry, it will be checked against the next ACL in the same sequence or the next sequence. If a flow does not match any ACL entry and at least one ACL is configured for that packet type, the packet is denied.